Ransomware attacks continue to evolve, often remaining undetected until files are already encrypted. While many organizations rely on endpoint protection and SIEM systems, one of the most valuable sources of early detection is often overlooked: backup telemetry.
Backup systems observe data change patterns across the entire infrastructure. Sudden changes in backup size, compression ratios, or restore point growth can indicate abnormal activity such as mass encryption.
By combining telemetry from Veeam Backup & Replication and VeeamONE with the analytics capabilities of Microsoft Fabric, organizations can build an AI-driven ransomware detection platform that identifies suspicious patterns before major damage occurs.
Why Backup Telemetry Is Ideal for Ransomware Detection
Backup systems continuously monitor data changes across servers, virtual machines, and repositories. This provides a unique vantage point for detecting abnormal behaviour.
Common ransomware signals in backup telemetry include:
- Sudden spikes in changed data blocks
- Rapid growth in backup size
- Compression ratio collapse
- Deduplication ratio reduction
- Simultaneous changes across many VMs
These indicators often appear hours before users notice encrypted files.
Architecture Overview
Having worked and supported Microsoft Fabric for over a year at Crayon, I was always integred with Microsoft Fabric’s capability. I saw an opportunity to see how Microsoft Fabric can integrate with Veeam. The solution architecture I came up with combines backup telemetry with cloud-scale analytics.
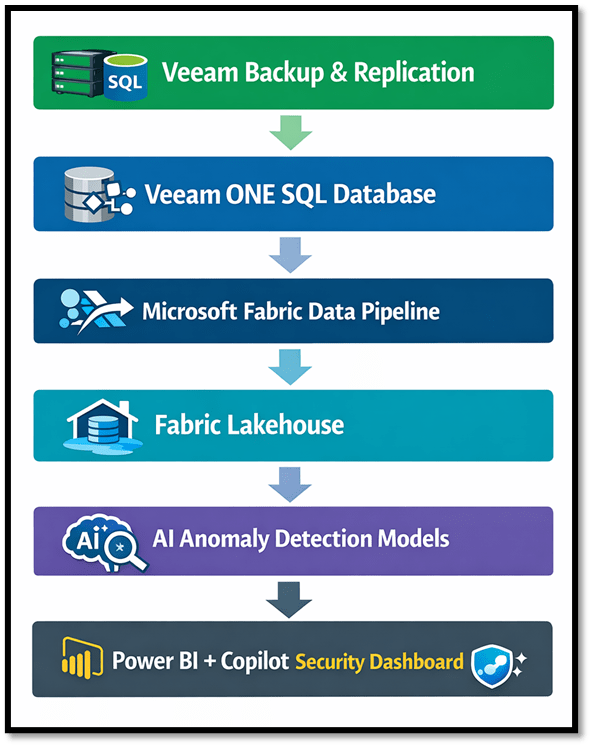
This architecture enables real-time security insights across the entire backup environment.
Ingesting Veeam Telemetry into Fabric
Telemetry data from VeeamONE can be extracted from its SQL database and ingested into a Fabric Lakehouse.
Key datasets include:
| Dataset | Description |
| Backup job sessions | Backup execution metrics |
| Restore points | Backup history per VM |
| Repository capacity | Storage consumption trends |
| VM inventory | Infrastructure metadata |
These datasets form the foundation of the analytics model.
AI Anomaly Detection Models
Once the telemetry data is available in Fabric, machine learning models can analyze patterns over time.
Examples of anomaly detection techniques include:
- Time series forecasting
- Z-score deviation analysis
- Isolation Forest models
- Seasonal trend analysis
These models help detect unusual backup behaviour such as abnormal data growth or compression anomalies.
Ransomware Risk Scoring per VM
To simplify detection, signals can be combined into a ransomware risk score for each VM.
Signals used in scoring:
- Backup size deviation
- Compression ratio drop
- Deduplication ratio change
- Restore point growth
- Repository growth spikes
Example scoring model:
RiskScore =
(SizeAnomaly * 0.35) +
(CompressionDrop * 0.25) +
(DedupDrop * 0.15) +
(RestorePointGrowth * 0.15) +
(RepositorySpike * 0.10)
VMs can then be classified as:
| Risk Score | Status |
| 0-30 | Normal |
| 30-60 | Suspicious |
| 60-80 | High risk |
| 80-100 | Critical |
Backup Entropy Analysis
Another powerful detection technique is entropy analysis (is a measure of the randomness, disorder, or unpredictability of data within a file. It is a critical metric used to identify packed, encrypted, or obfuscated malware, which often disguises itself as random data to evade detection).
Encrypted data has extremely high entropy due to its randomness. By sampling backup blocks and calculating Shannon entropy (measures the randomness, uncertainty, or information density within a dataset column), organizations can detect encryption activity.
Typical entropy values:
| Data Type | Entropy |
| Normal files | 5-7 |
| Compressed data | 7-7.8 |
| Encrypted data | 7.9-8 |
A sudden increase in entropy within backup datasets may indicate active encryption.
Immutable Backup Verification
Even with early detection, the most critical defence against ransomware remains immutable backups.
The analytics platform should continuously verify:
- Immutable repository status
- Object lock configuration
- Backup retention policies
- Hardened repository configuration
This ensures protected data cannot be altered or deleted during an attack.
AI-Powered Insights with Copilot
With the semantic model published in Power BI, Copilot can analyse telemetry and generate incident summaries.
Operations & Health example prompt:
“Summarise backup job failures over the last 30 days and identify the most common root causes.”
“Which backup jobs are trending towards failure based on duration and warning history?”
Security & Ransomware Readiness example prompt:
“Identify repositories with rapidly changing capacity patterns that could indicate ransomware activity.”
“Analyse backup telemetry anomalies detected in the last 24 hours and summarize potential ransomware indicators.”
“Show VMs without recent successful backups or restore points older than 7 days.”
SLA & Compliance example prompt:
“Which VMs are not meeting their RPO or SLA targets this month?”
“Generate an executive summary of data protection compliance for the last quarter.”
Capacity & Cost example prompt:
“Forecast backup repository capacity exhaustion based on the last 90 days of growth.”
“Which jobs and VMs consume the most backup storage?”
Executive Copilot prompt example prompt:
“Create an executive-level summary explaining the current state of backup health, risks, and recommended actions.”
Copilot can produce incident summaries including:
- Affected VMs
- Backup anomalies detected
- Repository impact
- Recommended response actions
This dramatically simplifies investigation and reporting.
Integrating with Security Operations
The platform can integrate with security tooling such as Microsoft Sentinel to trigger automated alerts when high-risk conditions are detected.
Example rule:
If VM Risk Score > 80
Trigger SIEM incident alert
This enables backup telemetry to become part of the broader security operations workflow.
Final Thoughts
Backup systems are traditionally viewed as a recovery tool, but they can also provide an incredibly valuable security intelligence layer.
By combining telemetry from Veeam Backup & Replication and VeeamONE with the analytics capabilities of Microsoft Fabric, organizations can build an AI-driven platform that detects ransomware signals early, validates backup protection, and automates security insights.
As ransomware continues to evolve, leveraging backup telemetry for proactive detection may become one of the most effective strategies in modern cyber resilience.
Published: March 20, 2026 04:40pm
Leave a comment